Cybersecurity Counter Reconnaissance: Impose a Cost to Attack
Cybersecurity Counter Reconnaissance: Impose a Cost to Attack
Crooks planning a local community bank robbery expose themselves to orders of magnitude more risk of life, limb and imprisonment than any random threat on the internet targeting the largest organizations on earth.
If you believe the above statement is true, which we know it to be, it's an absolutely perverse misalignment of risk. Think about all the successful breaches (at least the ones that were reported), the reputational and fiscal costs, and how many criminals get stopped, caught, or face any repercussions. It's a complete indictment of cybersecurity considering the global spend approaches between 1/4 and 1/2 trillion dollars depending on who you listen to. With that much spent on cybersecurity, why is it the case that, to this day, attacking is virtually free of cost and risk?
The reason is due to the innate attack/defense asymmetry that exists in cybersecurity. To summarize this: Defenders have to do everything perfectly, 24/7/365 in addition to keeping the lights on and turning a profit. Attackers, on the other hand, can sit in Grandma's basement on a VPN. They only have to find one foothold during a single point in time. With offensive AI capabilities increasing daily, this will continue to be the case as long as defenders use the same strategies they have always used.
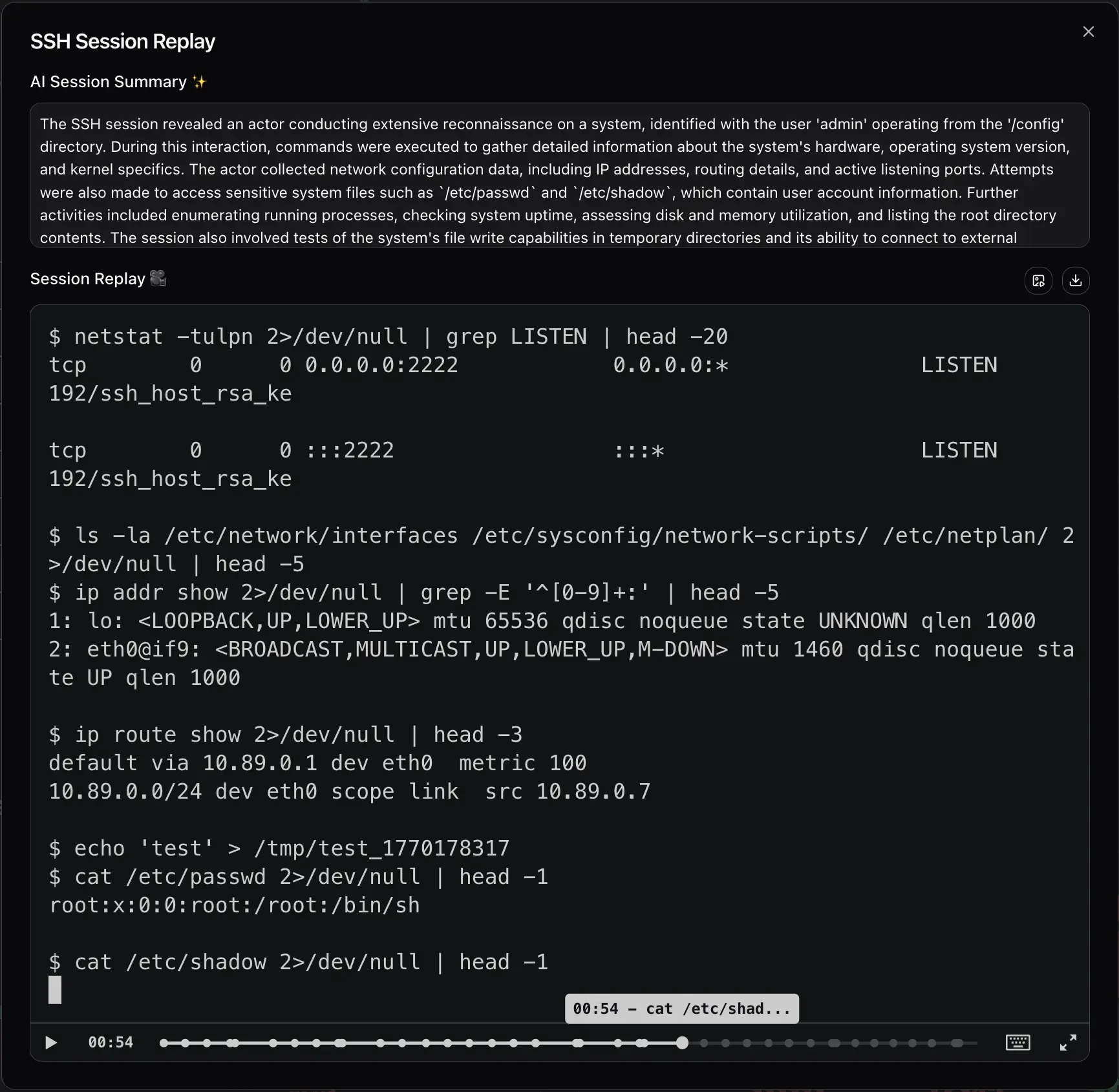
As long-time offensive operators, we want to offer a solution that actually turns the tables. Divert's goal is to flip this asymmetry to the defender's advantage: to make it so that attackers need to exercise continuous perfection, because if they make one mistake, they're burnt.
Cybersecurity counter reconnaissance is the earliest primitive in your security stack. Use what your adversary doesn't know against them. Which assets are real and which are landmines? Attackers are opportunists; hunting bugs on the edge is slim pickings. Attackers know by name, by look, and by feel which exposed services are better opportunities for footholds.
Attackers also have no pre-conceived notions about where assets live. It's 2026; there is no defined perimeter. Organizations have services deployed on premises, at AWS, at Google, at Microsoft, at CloudFlare, at Digital Ocean, and everywhere else. Attackers just want a foothold, to glean secrets, pivot, spread laterally, escalate privileges, and so forth.
Let's say you're ExampleCorp. You've got a lot of things in example.com. When attackers do initial recon against your DNS namespace they're going to look for the most enticing things first. What they don't know is that you've seeded a minefield on your edge. They see customerportal.example.com and customerportal-dev.example.com. They see vpn.example.com and vpn-backup.example.com. They see www.example.com and jump.example.com. Which ones do you figure are more interesting to an attacker?
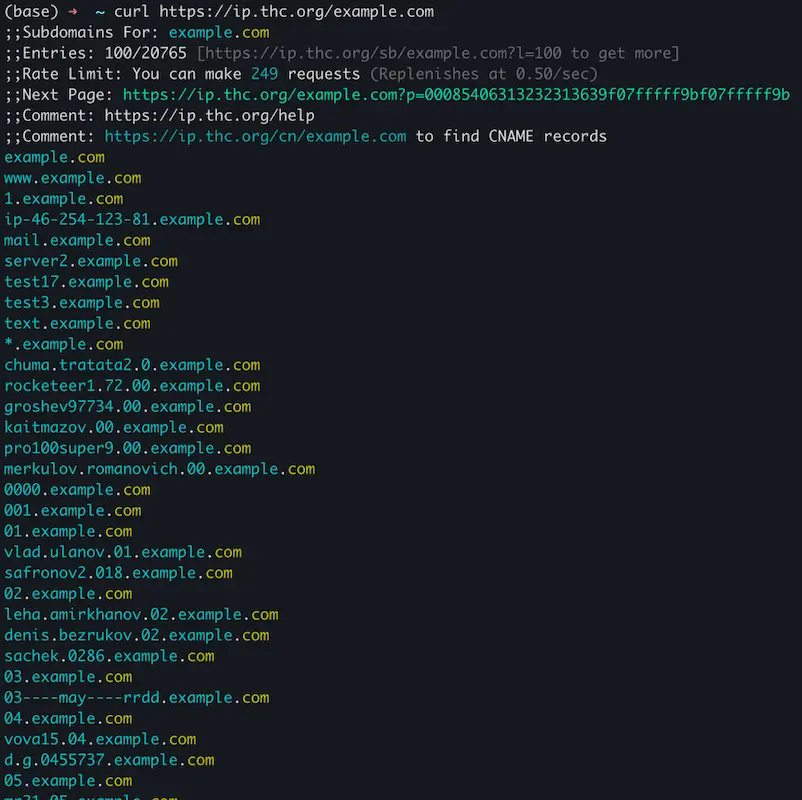
Organizations of any significant size have a mess of a DNS namespace: certs that expose names in crt.sh that might not even resolve and DNS hostnames of all varieties that resolve to IPs all over the place. If you don't believe me, check for yourself: https://ip.thc.org.
Wield this reality to your advantage: use what they don't know against them and impose a tax to attack you. Put the burden of flawless execution back on the offense, making them think twice.